Lazy Caturday Reads
Posted: March 16, 2019 Filed under: morning reads, U.S. Politics | Tags: anti-semitism, Bernie Sanders, Beto O'Rourke, cat gods and goddesses, Chelsea Clinton, Christchurch massacre, Cult of the Dead Cow, Donald Trump, hackers, Ilhan Omar, Islamophobia, mass shootings, Mikhail Lesin, murder fantasies, New Zealand, rape fantasies, terrorism 29 CommentsGood Morning!!
I said this a few days ago, and I’m still feeling it: I don’t want to live in this world. America’s toxic culture of white supremacy and mass shootings is spreading around the globe, enabled by Trump. I stayed offline for much of the day yesterday so I wouldn’t have to read about the horror in New Zealand.
I did hear last night that somehow the massacre on the other side of the world was the fault of Chelsea Clinton. At least according to some Bernie Sanders supporters. Here’s the video of a young women in a Bernie T-shirt poking her finger at Chelsea and screaming in her face.
https://twitter.com/girlsreallyrule/status/1106752139404075010
Clinton, who attended and worked at the university in various capacities, including co-founding the Of Many Institute for Multifaith Leadership, was said to be invited to the vigil, according to students at the vigil.
But Clinton’s presence at the vigil was not a welcome sight for at least two activists who were at the vigil.
A video went viral on Twitter Friday night showing a confrontation between Clinton and a student activist, filmed and tweeted out by a friend, who can be seen in the video telling Clinton, “This right here is the result of a massacre stoked by people like you and the words that you put into the world. And I want you to know that and I want you to feel that deeply — 49 people died because of the rhetoric you put out there.” [….]
On Twitter, an account that appears to belong to the student activist wrote, “the CAUCASITY that chelsea clinton has showing up to a vigil for the 49 muslims massacred in an islamophobic hate crime after STOKING ISLAMOPHOBIA AND RACISM surrounding ilhan omar… f—ing ridiculous.” The account retweeted the video, posted by her “best friend,” writing, “apparently my brand is yelling at white politicians.”
Fact check: Chelsea Clinton is not a politician. Chelsea’s offense was that she sent a tweet about anti-semitism, after which she politely interacted with Rep Ilhan Omar, who had been criticized for tweets about politicians supporting Israel because they received donations from AIPAC. Here is what Clinton tweeted: “We should expect all elected officials, regardless of party, and all public figures to not traffic in anti-Semitism.”
On the other hand, let’s take a look at Trump’s history. Brian Klaas at The Washington Post: A short history of President Trump’s anti-Muslim bigotry.
Trump’s anti-Muslim bigotry has a long history. In 2011 and 2012, Trump insinuated that President Barack Obama was secretly Muslim. In September 2015, at a campaign rally, Trump nodded along as a supporter claimed “we have a problem in this country; it’s called Muslims.” Trump continued nodding, saying “right,” and “we need this question!” as the supporter then proceeded to ask Trump “when can we get rid of them [Muslims]?” In response, Trump said: “We’re going to be looking at a lot of different things.”
In November 2015, on “Morning Joe,” Trump said that America needs to “watch and study the mosques.” Four days later, he indicated that he would “certainly implement” a database to track Muslims in the United States. Two days after that, he falsely claimedthat “thousands and thousands” of Muslims cheered in New Jersey when the World Trade Center collapsed on Sept. 11, 2001.
Then came the most egregious statement — one that should haunt Trump’s legacy forever and taint everyone who supported him subsequently: On Dec. 7, 2015, he called to ban all Muslims from entering the United States. Three days later, Trump tweeted that the United Kingdom is “trying hard to disguise their massive Muslim problem.” On March 9, 2016, Trump falsely claimed that “Islam hates us.”
Upon taking office, Trump surrounded himself with anti-Muslim bigots. Sebastian Gorka, a former Trump adviser, was fired by the FBI for his Islamophobia. Michael Flynn, Trump’s disgraced national-security-adviser-turned-felon, said that Islam “is like a cancer.” And top officials such as Secretary of State Mike Pompeo and national security adviser John Bolton have also stoked hatred of Islam.
In late November 2017, Trump retweeted three videos by Jayda Fransen. She was one of the leaders of Britain First, a neo-fascist hate group. She has been convicted of multiple hate-crime offensesand was involved in organizing “Christian patrols,” which included what Britain First called “mosque invasions” aimed at intimidating British Muslims. While Fransen was out on bail, she appeared on Radio Aryan, a neo-Nazi radio station. Her interview began right after the station concluded its reading from “Mein Kampf.” That is who the president of the United States chose to amplify to his millions and millions of Twitter followers.
There’s much more at the link if you can stand to read it.
More from Vox: The New Zealand shooter called immigrants “invaders.” Hours later, so did Trump.
President Donald Trump just used similar language to describe immigrants coming into the United States that the alleged mass shooter did to justify killing nearly 50 Muslims in Christchurch, New Zealand.
On Friday, Trump issued the first veto of his presidency to override a congressional blockade of the national emergency he declared at America’s southern border. During the veto signing ceremony, Trump explained why he felt a national emergency was warranted to stop migrants from entering the US.
“People hate the word ‘invasion,’ but that’s what it is,” he said, according to the White House pool report.
That is chillingly similar to the language the main suspect in Friday’s Christchurch terrorist attack used to explain why he chose to gun down at least 49 Muslims. In the rambling 74-page manifesto the 28-year-old suspected shooter posted online shortly before the attack, he writes that he was committing the killings “to show the invaders that our lands will never be their lands.”
It’s also the same language the man who killed 11 people at a synagogue in Pittsburgh last October used: In that case, the perpetrator blamed Jews for helping what he called “invaders”in the Central American migrant caravans who were trying to enter the US.
Informative articles on the New Zealand terrorist attack, links only:
David C. Atkinson at The New Republic: The Longer History of the Christchurch Attacks. For over a century, the United States has played a role in inspiring and enabling white supremacy in Australia and New Zealand.
Wajahat Ali at The New York Times: The Roots of the Christchurch Massacre. All those who have helped to spread the worldwide myth that Muslims are a threat have blood on their hands.
NBC News: New Zealand shooting leaves online extremism researchers ‘hopeless and furious.’
The Daily Beast: New Zealand Mosque Shooting Suspect Used Swedish Girl’s Death as License to Kill.
More interesting reads to check out
Radio Free Europe/Radio Liberty has a fascinating story on that former Putin pal who supposedly died accidentally in a DC hotel room: Exclusive: Washington Autopsy Files Reveal Lesin Sustained Broken Bone In Neck.
WASHINGTON — Mikhail Lesin, the former Russian press minister who turned up dead in a Washington hotel room in 2015, sustained a fracture to a neck bone just below the jaw line “at or near the time” of his death, according to documents released by the city’s medical examiner that provide new details about his final days….
That detail, however, and others contained in the 149-page file released exclusively to RFE/RL offer the most precise scientific description to date about Lesin’s death, which officials ruled accidental and said was caused by blunt-force injuries amid excessive alcohol consumption.
Once a powerful media adviser to President Vladimir Putin, Lesin fell out of favor with the Kremlin elite sometime around 2012 and had lowered his public profile before he was discovered dead in the Dupont Circle Hotel, located a few blocks from the White House, on November 5, 2015….
Among the new details revealed by the documents:
• Lesin’s hyoid — a bone located about midway between the larynx and the jaw bone — was completely fractured;
• The FBI considered possibly taking over the case in early 2016. It wasn’t clear whether the agency formally did so, though earlier files released by the agency show its agents were involved in questioning witnesses and examining video recordings from hotel cameras;
• Lesin’s son, Anton, who lives in Beverly Hills, California, told investigators he did not know why his father was in the U.S. capital, and also reported that Lesin regularly had serious bouts of drinking while on business trips;
• The day after the Office of the Chief Medical Examiner released an initial report, one of its officials was summoned to appear before a criminal grand jury looking into Lesin’s death;
• In a report filed the day of Lesin’s death, a forensic investigator with the Office of the Chief Medical Examiner wrote that a detective had called and said a “friend” of the former Russian official had contacted him and “inquired about the decedent’s location.”
Read many more details at the link.
The media has begun vetting Beto O’Rourke. Two interesting reads:
Reuters: Beto O’Rourke’s secret membership in America’s oldest hacking group.
While a teenager, O’Rourke acknowledged in an exclusive interview, he belonged to the oldest group of computer hackers in U.S. history.
The hugely influential Cult of the Dead Cow, jokingly named after an abandoned Texas slaughterhouse, is notorious for releasing tools that allowed ordinary people to hack computers running Microsoft’s Windows. It’s also known for inventing the word “hacktivism” to describe human-rights-driven security work.
Members of the group have protected O’Rourke’s secret for decades, reluctant to compromise his political viability. Now, in a series of interviews, CDC members have acknowledged O’Rourke as one of their own. In all, more than a dozen members of the group agreed to be named for the first time in a book about the hacking group by this reporter that is scheduled to be published in June by Public Affairs. O’Rourke was interviewed early in his run for the Senate.
There is no indication that O’Rourke ever engaged in the edgiest sorts of hacking activity, such as breaking into computers or writing code that enabled others to do so. But his membership in the group could explain his approach to politics better than anything on his resume. His background in hacking circles has repeatedly informed his strategy as he explored and subverted established procedures in technology, the media and government.
“There’s just this profound value in being able to be apart from the system and look at it critically and have fun while you’re doing it,” O’Rourke said. “I think of the Cult of the Dead Cow as a great example of that.”
That doesn’t seem to problematic to me. As younger candidates come forward, they are likely to have on-line histories. This story from Politico is a bit more embarrassing: O’Rourke ‘not … proud’ of teenage murder fantasy writing.
Beto O’Rourke said Friday he is “not … proud” of fiction he wrote as teenager about murdering children, while acknowledging its surfacing could hurt his campaign.
“Stuff I was part of as a teenager … not anything that I’m proud of today,” O’Rourke told reporters outside a meet-and-greet here. “And I mean, that’s the long and short of it.”
O’Rourke’s remarks followed a report in Reuters that O’Rourke, as a young member of the computer hacking group Cult of the Dead Cow, wrote an online article about how society could work without money and, in a more disturbing missive, about killing children.
“One day, as I was driving home from work, I noticed two children crossing the street. They were happy, happy to be free from their troubles. … This happiness was mine by right. I had earned it in my dreams,” he wrote, according to Reuters. “As I neared the young ones, I put all my weight on my right foot, keeping the accelerator pedal on the floor until I heard the crashing of the two children on the hood, and then the sharp cry of pain from one of the two. I was so fascinated for a moment, that when after I had stopped my vehicle, I just sat in a daze, sweet visions filling my head.”
There’s more of this stuff, definitely creepy; but it was a long time ago. Bernie Sanders survived his early fantasy writings about rape and his theories about breast cancer being caused by sexual frustration.
What else is happening? What stories are you following today?
Thursday Reads: Updates from Snowden-Greenwald Land and Other News
Posted: May 22, 2014 Filed under: morning reads | Tags: Cincinnatus, cyber-parties, discrimination, Edward Snowden, encryption extremists, George Packer, Glenn Greenwald, hackers, Jacob Applebaum, Julian Assange, Kevin Poulsen, Laura Poitras, NSA, Poverty, privacy extremists, Racism, Runa Sandvik, Sexism, The Tor Project, unemployment, Wikileaks 32 CommentsGood Morning!!
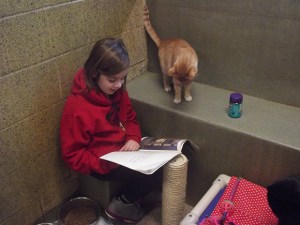
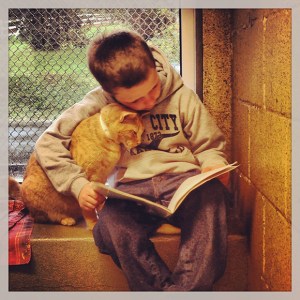
The photos in today’s post are from a project by photographer Mark Makela to take pictures of children “learning to read by reading to homeless cats.”
Last February, photographer Mark Makela traveled to Birdsboro, Pennsylvania, to photograph a reading group where the participants were grade-school students and a group of cats. The idea for the group, known as Book Buddies, was hatched at the Animal Rescue League of Berks County when the program coordinator Kristi Rodriguez’s 10-year-old son was struggling with reading. Rodriguez decided to bring him into the shelter, where he could be in what she called a “nonevaluative” environment in order to feel more comfortable practicing his reading skills. It worked.
According to ARL’s website, studies at Tufts University found that the more relaxed, nonjudgmental audience of cats helps students to sustain their focus, maintain a higher state of awareness, and develop an improved attitude toward school. In August of last year, ARL officially started the Book Buddies program, inviting students in first through eighth grades to read to the cats. As an incentive to continue, once the students complete five books, they receive prizes. “It’s one of those opportunities that is unique and humorous and so endearing,” Makela said about the assignment to document the Book Buddies program.
See more marvelous photos at the Slate Magazine link above. Even more at Buzzfeed–including more girls.
Now to the news:
I’ve long suspected that Edward Snowden interacted with Wikileaks’ Julian Assange and others in the hacker community before he made his final decision to steal a massive trove of data from NSA computers and then abscond to Hong Kong at the end of May last year.
We know that Snowden was in touch with Jacob Applebaum and Laura Poitras early on, because they published an interview with him in Der Spiegel that they had conducted by e-mail in Mid-May, before Snowden fled Hawaii. But Snowden could have actually met Applebaum in Hawaii in April 2013 when Applebaum vacationed there by his own admission. Did Snowden and Applebaum discuss Snowden’s plans to steal NSA files? Did Applebaum suggest which items Snowden should take? Note that Applebaum is deeply involved with Wikileaks and has been a long-time, passionate defender of Julian Assange.
Glenn Greenwald revealed in his new book “No Place to Hide” that Snowden had used the code name “Cincinnatus” in early communications between the two. Interestingly enough, a “cyber-party” had been held in Hawaii in December 2012, and the host was someone who called himself “Cincinnatus.” Once this news came out, people began speculating on Twitter that perhaps this wasn’t a coincidence. Suddenly, on May 17, the cyber-party announcement was deleted by someone with the Twitter handle @jskuda. Fortunately Twitter user @ShrillBrigade located it on the Wayback Machine. And check out the title of Cincinnatus’ talk: “Painlessly setting up your own fast exit.” (h/t @catfitz)
Then yesterday, former criminal hacker and technical adviser to Greenwald and Poitras’ Freedom of the Press Foundation Kevin Poulsen published a limited hangout at Wired: Snowden’s First Move Against the NSA Was a Party in Hawaii.
It was December 11, 2012, and in a small art space behind a furniture store in Honolulu, NSA contractor Edward Snowden was working to subvert the machinery of global surveillance.
Snowden was not yet famous. His blockbuster leaks were still six months away, but the man destined to confront world leaders on a global stage was addressing a much smaller audience that Sunday evening. He was leading a local “Crypto Party,” teaching less than two dozen Hawaii residents how to encrypt their hard drives and use the internet anonymously.
“He introduced himself as Ed,” says technologist and writer Runa Sandvik, who co-presented with Snowden at the event, and spoke about the experience for the first time with WIRED. “We talked for a bit before everything started. And I remember asking where he worked or what he did, and he didn’t really want to tell.”
Runa Sandvik is a hacker who works at the TOR project along with Jacob Applebaum. TOR is a site (ironically funded by the U.S. Department of Defense) that provides free encryption software to people who want to hide their on-line activities (including drug dealers and child porn purveyors).
Poulsen writes:
The roots of Snowden’s crypto party were put down on November 18, 2012, when he sent an e-mail to Sandvik, a rising star in privacy circles, who was then a key developer on the anonymous web surfing software Tor.
Tor is free software that lets you go online anonymously. The software is used by a wide swath of people in need of extreme anonymity, including human rights groups, criminals, government agencies, and journalists. It works by accepting connections from the public internet, encrypting the traffic and bouncing it through a winding series of relays before dumping it back on the web through any of more than 1,000 exit nodes.
Most of those relays are run by volunteers, and the pre-leak Edward Snowden, it turns out, was one of them.
How about that? Snowden was already deeply involved with TOR in December 2012–and Jacob Applebaum of TOR just happened to travel to Hawaii a few months later in April! Coincidence? I don’t think so.
In his e-mail, Snowden wrote that he personally ran one of the “major tor exits”–a 2 gbps server named “TheSignal”–and was trying to persuade some unnamed coworkers at his office to set up additional servers. He didn’t say where he worked. But he wanted to know if Sandvik could send him a stack of official Tor stickers. (In some post-leak photos of Snowden you can see the Tor sticker on the back of his laptop, next to the EFF sticker).
Well, well, well. Now we know how Snowden got his TOR sticker. Did Runa give him the EFF sticker too? Read the rest of the Wired piece for more details.
Phew! I hope that made sense. This stuff is difficult to write about.
Also yesterday, well-known and respected journalist and New Yorker writer George Packer published a no-holds-barred review of Glenn Greenwald’s new book in the UK Prospect: The errors of Edward Snowden and Glenn Greenwald. Among other things, Packer accuses Greenwald of “a pervasive absence of intellectual integrity,” and provides numerous examples. He characterizes Snowden as someone who lives on the internet, detached from the realities of the real world. Here are a few excerpts, but please read the whole thing.
Snowden’s leaks can be seen, in part, as a determined effort to restore the web to its original purity—a project of technology rather than law. “Let us speak no more of faith in man, but bind him down from mischief by the chains of cryptography,” wrote Snowden, in an early message to his collaborators. In March of this year, appearing remotely from Russia on a robotised screen onstage at a TED talk in Vancouver, Snowden said that the single best solution to the NSA’s abuses is stronger encryption: “The internet that we’ve enjoyed in the past has been exactly what we, as not just a nation but as a people around the world, need.” In taking nearly two million highly classified documents from the US, he was grabbing back the key to heaven.
As I’ve written previously, Snowden’s solution to the problem of government interference with its citizens is impenetrable universal encryption–never mind the fact that this would allow vast numbers of vicious criminals to hide their actions from law enforcement.
As I suspected, Packer writes that Greenwald’s book “contains no major scoops.” He does, however, praise Greenwald’s argument for the primacy of privacy as central to a “free society.”
Greenwald also makes a powerful case—all the more so for being uncompromising and absolute—for the central role of privacy in a free society, and against the utilitarian argument that, since the phone companies’ metadata on Americans hasn’t been seriously abused by government officials (not yet, anyway), none of us should be too worried. In a chapter called “The Harm of Surveillance,” he cites Justice Louis Brandeis’s famous opinion on the basic “right to be let alone,” and writes: “The desire for privacy is shared by us all as an essential, not ancillary, part of what it means to be human. We all instinctively understand that the private realm is where we can act, think, speak, write, experiment, and choose how to be, away from the judgemental eyes of others. Privacy is a core condition of being a free person.”
I would argue that these considerations are of vital importance to people like Greenwald who are financially secure. Those Americans who must deal with racial and gender discrimination, long-term unemployment, and especially grinding poverty have other, more urgent concerns. Can one be a “free person” under those conditions?
Along similar lines, Packer writes:
If Greenwald and others were actually being persecuted for their political beliefs, they would instinctively understand that the rule of law has to protect people regardless of politics. The NSA disclosures are disturbing and even shocking; so is the Obama administration’s hyper-aggressive pursuit of leaks; so is the fact that, for several years, Poitras couldn’t leave or re-enter the US without being questioned at airports. These are abuses, but they don’t quite reach the level of the Stasi. They don’t portend a totalitarian state “beyond the dreams of even the greatest tyrants of the past,” as Greenwald believes is possible. A friend from Iran who was jailed and tortured for having the wrong political beliefs, and who is now an American citizen, observed drily, “I prefer to be spied on by NSA.” The sense of oppression among Greenwald, Poitras, and other American dissenters is only possible to those who have lived their entire lives under the rule of law and have come to take it for granted.
In the year since the first NSA disclosures, Snowden has drifted a long way from the Thoreauvian ideal of the majority of one. He has become an international celebrity, far more championed than reviled. He has praised Russia and Venezuela’s devotion to human rights. His more recent disclosures have nothing to do with the constitutional rights of US citizens. Many of them deal with surveillance of foreign governments, including Germany and Brazil, but also Iran, Russia, and China. These are activities that, wise or unwise, fall well within the NSA’s mandate and the normal ways of espionage. Snowden has attached himself to Wikileaks and to Assange, who has become a tool of Russian foreign policy and has no interest in reforming American democracy—his goal is to embarrass it. Assange and Snowden are not the first radical individualists to end up in thrall to strongmen.
Snowden looked to the internet for liberation, but it turns out that there is no such thing as an entirely free individual. Cryptography can never offer the absolute privacy and liberty that Snowden seeks online. The internet will always be a space controlled by corporations and governments, and the freedom it provides is of a limited, even stunting, kind. No one lives outside the fact of coercion—there is always a state to protect or pursue you, whether it’s Obama’s America or Putin’s Russia.
I’ve barely touched the surface of Packer’s scathing critique of Greenwald’s “journalism”; I enourage you to go to Prospect link to read more.
I have a few more stories for you that I’ll list link-dump style:
It appears that the prosecution in the Boston Bombing case decided to leak some previously secret information–most likely to counter the defense’s argument that Dzhohar Tsarnaev was illegally questioned by the FBI when he was in the hospital with terrible injuries.
Reuters: Accused Boston bomber admitted role in attack, prosecutors say
NBC News: Government doc shows how closely Boston Marathon bombers followed al Qaeda plans.
NY Daily News: Boston Marathon bombers used ‘sophisticated’ bombs made of parts from Christmas lights, model cars: prosecutors.
Boston Globe: Christmas Lights Used in Boston Marathon Bombs.
KSDK.com: Feds: Boston bomber’s hideout note says he wanted to be martyr.
ABC News: FBI Feared Boston Bombers ‘Received Training’ And Aid From Terror Group, Docs Say.
This is encouraging from the Boston Globe: Oakland Examining Pension of FBI Agent who Shot Todashev
Other News:
The Economic Times of India: Google wants to show ads through your thermostat and car. (You though the NSA was bad?)
Information Week: Google Outlines Advertising Vision. (How would you like targeted Google ads appearing on your refrigerator or watch?)
The Atlantic: It Wasn’t Household Debt That Caused the Great Recession; It was how that debt was disproportionately distributed to America’s most economically fragile communities.
NYT: U.S. Sends Troops to Chad to Aid Hunt for Nigerian Schoolgirls.
USA Today: Thai military declares coup, detains party leaders.
Science Recorder: ‘Aliens of the sea’ could lead to breakthroughs in regenerative medicine.
What stories are you following today? Please post your links on any topic in the comment thread.
Tuesday Reads: Hacker Twitter Storm and Post-Prom Nightmares
Posted: May 20, 2014 Filed under: Crime, morning reads, Rape Culture, Real Life Horror, Violence against women | Tags: after-prom horrors, Calhoun High School Georgia, cypherpunks, Edward Snowden, Ellijay Georgia Calhoun High Prom Rape, gang rape, Gilmer County GA, Glenn Greenwald, hackers, Jacob Applebaum, John Cook, Laura Poitras, NSA leaks, redactions, The Intercept, twitter fight, twitter storm 104 Comments
Good Morning!!
In the comments on yesterday’s post, I mentioned that there has been quite a bit of tension building up between Glenn Greenwald and some of the more extreme members of the (for lack of a better name) cypherpunks crowd–Wikileaks, Cryptome.com, and the hacker community (including Jacob Applebaum, who is closely involved both with Wikileaks and Laura Poitras, Greenwald’s partner in crime. I guess I should have stayed up later last night, because this morning I woke up to the aftermath of a major storm in the Twitterverse, where most of these types of people choose to communicate with each other.
The fight stemmed from an article posted at The Intercept yesterday, in which the authors chose to redact the name of one of the five countries targeted by NSA data collection. However, it really goes back much further than that.
There has been a long running disagreement between Greenwald and the other groups I mentioned on how much of Edward Snowden’s trove of stolen NSA data to publish. The hacker/Wikileaks crowd thinks Greenwald should simply release everything and let the chips fall where they may, and Greenwald claims he is carefully vetting the material with Snowden’s help in order not to reveal anything that would harm anyone.
Greenwald has actually revealed only a small portion of the material so far, presumably holding back information that he wanted to include in his book. But now the book has been released, and it apparently contains much information that has already been published. For those who have been obsessively following the NSA leaks story, there doesn’t seem to be a need to buy the book. Why is Greenwald being so stingy?
Here’s some background from Michael Kelley at Business Insider: WikiLeaks Threatens To Reveal Information That Glenn Greenwald Says Could Lead To ‘Deaths’.
America’s National Security Agency (NSA) can “vacuum up and store the actual content of every conversation” in the Bahamas and an unnamed country, the new publication The Intercept reported Monday, based on documents leaked by Edward Snowden.
Intercept Editor Glenn Greenwald — who wrote about documents leaked by Snowden when he was a columnist for The Guardian — said the publication didn’t reveal the country because it was “very convinced” that doing so would lead to “deaths.”
After a heated discussion between WikiLeaks, Greenwald, Intercept Editor-In-Chief John Cook, and American WikiLeaks hacker-turned-Der Spiegal contributor Jacob Appelbaum, WikiLeaks tweeted that it will reveal the name of the second country being spied on by the NSA.
As Kelley points out, the implications is that Wikileaks knows the name of the country either by unmasking the redaction with software or because Wikileaks has access to the Snowden files.
The most plausible way for WikiLeaks to have access to a Snowden cache is if Appelbaum, who led the reporting on several Der Spiegel articles based on NSA documents (which may or may not be from Snowden), shared information with his friend and WikiLeaks Editor-In-Chief Julian Assange. Applebaum tweeted that The Intercept’s redaction was “a mistake.”
Appelbaum, a close friend of Laura Poitras, the other journalist whom Snowden gave a large set of documents, also gave a presentation detailing a classified document listing technology available to the NSA’s hacking unit, known as TAO. It is not known how he acquired those documents.
So which is it? The careless ways in which the Snowden documents have been passed around between The Guardian and The New York Times and other news organizations; with Greenwald’s husband David Miranda carrying them through London to Berlin and back; as well as the fact that Snowden is in Russia, suggest that the entire cache will eventually be released, and presumably all hell will break loose. It’s only a matter of time.
Charles Johnson posted the entire Wikileaks-Greenwald argument at Little Green Footballs: Slap Fight of the Day: Wikileaks vs Pernicious G
Today on Twitter this happened: Julian Assange, who most people believe is the one behind the @Wikileaks account, threw a huge tantrum because Glenn Greenwald redacted the name of a country from his latest disingenuous article. Greenwald says he was convinced publishing the country’s name would lead to deaths. Assange doesn’t give a shit about that, of course.
There are some inadvertently hilarious moments here; Wikileaks’s Jacob Appelbaum says redacting the country “makes Wikileaks look extreme.” I almost fell out on that one. And then there’s the tweet in which Assange basically calls everyone in Greenwald’s crew “a bunch of racists.” And it all ends with Assange issuing a super-villain threat to release the country’s name “in 72 hours.”
Scroll through the collection below to see what it looks like when extreme libertarians have a purity war.
Head over to Green Footballs if you want the details. Read more exchanges between Wikileaks, Jacob Applebaum, and John Cook, editor of The Intercept at Chirpstory. Read more at Buzzfeed, where Miriam Berger and Miriam Elder provide a timeline of the tweets along with their interpretation: Julian Assange Is Angry At Glenn Greenwald And He’s Not Going To Take It Anymore.
Finally, Bob Cesca’s take on the whole affair: The Wikileaks vs Greenwald Twitter Fight: Julian Assange Threatens To Reveal Deadly NSA Info.
It all began Monday morning when The Intercept posted a new Snowden revelation with cutesy headline: “Data Pirates of the Caribbean: The NSA Is Recording Every Cell Phone Call in the Bahamas.” Get it? Pirates! The article exhaustively describes an operation called MYSTIC and another called SOMALGET in which NSA gathers audio and metadata of cellphone calls in the Bahamas in order to spy on human traffickers and drug cartels. The Bahamas is notorious for both.
Naturally, the article featured all of the deceptive Greenwaldian bait-and-switch we’ve come to expect from his Snowden articles. For example, in paragraph seven, Greenwald and his co-authors Ryan Devereaux and Laura Poitras noted that Sen. Tom Harkin (D-IA), Bill Gates and Oprah Winfrey routinely vacation in the Bahamas:
By targeting the Bahamas’ entire mobile network, the NSA is intentionally collecting and retaining intelligence on millions of people who have not been accused of any crime or terrorist activity. Nearly five million Americans visit the country each year, and many prominent U.S. citizens keep homes there, including Sen. Tom Harkin (D-Iowa), Bill Gates, and Oprah Winfrey.
NSA is spying on Oprah! Stop the presses! But no, if you read all the way down to the 54th paragraph (!!) Greenwald tosses in a token mention of NSA’s rules about preventing data collection against U.S. Persons, whether or not they happen to be inside the U.S. There are very strict “minimization” procedures to eliminate the data that might’ve been inadvertently collected. Why? Because it’s illegal to spy on Americans without an individual warrant. And, by the way, Greenwald & Company noted that the SOMALGET program is, yes, legal.
It sure seems like there are enough hints in the story for anyone to guess the redacted country. Pirates? SOMALGET? Plus the fact the Assange accused Greenwald of “racism.” Read much more interpretation and more tweets at The Daily Banter.
I’ll be keeping a close eye on this story from now on and I’ll pass on any new information.
In other news . . .
On Sunday JJ wrote about an alleged gang rape that reportedly took place after the Calhoun High School senior prom in North Georgia on May 10. The reason I’m writing about it is that Sky Dancing has been getting a huge number of clicks from people looking for more information on this story. It seems people want to know what is happening, but the local papers have not published anything on the crime or the investigation since Sunday. Doesn’t that seem odd and troubling? Is a cover-up in the works. As JJ pointed out it brings back memories of Steubenville, Ohio. After the gang rape there, local officials tried to sweep it under the rug, but a blogger and an “Anonymous” group kept the story alive. Maybe someone with inside information from Calhoun needs to get something like that started? As in Steubenville, there are hints that coddled football players may be involved.
Meanwhile, in another prom-related tragedy, a girl was found dead after a prom at MacArthur High School in Houston. According to her mother, the mother of Jacqueline Gomez’ boyfriend was supposed to bring her home that night, but instead the boy’s mother allowed the couple to stay in a hotel room against the Gomez’ mother’s wishes. To me the whole thing sounds really suspicious. From KHOU.com, Mother: Daughter was not supposed to stay at hotel after MacArthur HS prom.
There are new startling details from the mother of a teenagerfound dead on prom night. Her mother feels like she was mislead by her daughter’s prom date and his mother….
Gomez was off to her senior prom at the Hyatt North Houston Hotel. Her mother was too distraught to show her face on camera, but said she expected to see her daughter back at home later that night….
Barron said Gomez’s date’s mother picked the couple up from her home. She also picked them up from the hotel later that night. That’s when she last spoke to her daughter on the phone.
“I just spoke to them after prom, a couple words, told me she was going to get something to eat,” said Barron.
That’s when the boy’s mother got on the phone and asked if Gomez could spend the night at their house.
“I said no, bring her back home,” said Barron. “I gave them a couple hours, and I never heard back.”
The next call she got was from a homicide detective with the Houston Police Department. She said detectives told her the room was booked by the boyfriend’s mother.
What happened? Who gave Jacqueline the drugs and did the boy’s mother know about it? More information from The Houston Chronicle: Texts Hint Girl May Have Overdosed After Prom.
A series of text messages offered new details into the death of Jacqueline Gomez, the 17-year-old Aldine ISD senior found dead Saturday in a Houston motel room the morning after her prom. The texts, sent from an account identified as Gomez’s date, also indicate investigators believe the girl probably overdosed….
Yet nobody can be certain how the MacArthur High School student died until autopsy results are complete – which could take several weeks, the Harris County medical examiner said. And that has the date and Gomez’s family and friends anxiously waiting for the mystery to be solved.
Meanwhile, her friends and family refute any suggestion that Gomez was ever a “party girl,” saying she spent most of her time working at a Kroger grocery and preparing to graduate in June.
Was Jacqueline given a date-rape drug? We may never find out, because those drugs wash out of the system very quickly. Check this out:
“He was posting pictures of himself crying on Instagram. So I a sent him a text that day to ask what had happened to my girl,” said Justice Gonzalez, a close friend of Gomez who saw the couple leave the prom together Friday night to go to that room. Authorities report Gomez was found dead in her bed about 9:20 the next morning.
“They said she overdosed,” part of the text reads, likely referring to law enforcement officials.
He went on.
“I woke up. I tried waking her but she wouldn’t,” the date texted back, adding four frowning faces. “I was screaming and crying telling her to wake up. But she didn’t. She didn’t,” He ended his text with two frowning faces with tears.
He stated she had appeared “perfectly fine and happy” when they left the “Miami Night” prom. She also seemed “happy” when they both went to sleep, he said.
He had told authorities that they had some alcohol, but said in a text to the friend that Gomez had also taken the painkiller hydrocodone.
Why the f&ck didn’t didn’t he take her home, and WTF was his mother thinking?! Furthermore, why can’t something be done to prevent these kinds of after-prom horrors?
Now I’m really mad, and I’m running out of space and time. I’ll post links to other news in the comment thread, and I hope you’ll do the same.


























Recent Comments