Thursday Reads: Updates from Snowden-Greenwald Land and Other News
Posted: May 22, 2014 Filed under: morning reads | Tags: Cincinnatus, cyber-parties, discrimination, Edward Snowden, encryption extremists, George Packer, Glenn Greenwald, hackers, Jacob Applebaum, Julian Assange, Kevin Poulsen, Laura Poitras, NSA, Poverty, privacy extremists, Racism, Runa Sandvik, Sexism, The Tor Project, unemployment, Wikileaks 32 CommentsGood Morning!!
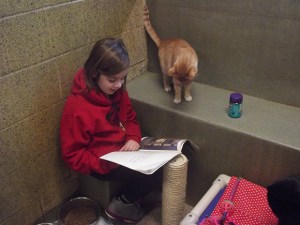
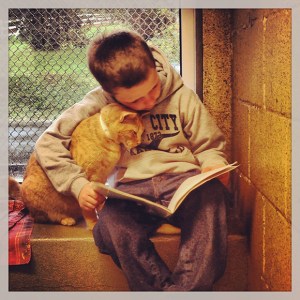
The photos in today’s post are from a project by photographer Mark Makela to take pictures of children “learning to read by reading to homeless cats.”
Last February, photographer Mark Makela traveled to Birdsboro, Pennsylvania, to photograph a reading group where the participants were grade-school students and a group of cats. The idea for the group, known as Book Buddies, was hatched at the Animal Rescue League of Berks County when the program coordinator Kristi Rodriguez’s 10-year-old son was struggling with reading. Rodriguez decided to bring him into the shelter, where he could be in what she called a “nonevaluative” environment in order to feel more comfortable practicing his reading skills. It worked.
According to ARL’s website, studies at Tufts University found that the more relaxed, nonjudgmental audience of cats helps students to sustain their focus, maintain a higher state of awareness, and develop an improved attitude toward school. In August of last year, ARL officially started the Book Buddies program, inviting students in first through eighth grades to read to the cats. As an incentive to continue, once the students complete five books, they receive prizes. “It’s one of those opportunities that is unique and humorous and so endearing,” Makela said about the assignment to document the Book Buddies program.
See more marvelous photos at the Slate Magazine link above. Even more at Buzzfeed–including more girls.
Now to the news:
I’ve long suspected that Edward Snowden interacted with Wikileaks’ Julian Assange and others in the hacker community before he made his final decision to steal a massive trove of data from NSA computers and then abscond to Hong Kong at the end of May last year.
We know that Snowden was in touch with Jacob Applebaum and Laura Poitras early on, because they published an interview with him in Der Spiegel that they had conducted by e-mail in Mid-May, before Snowden fled Hawaii. But Snowden could have actually met Applebaum in Hawaii in April 2013 when Applebaum vacationed there by his own admission. Did Snowden and Applebaum discuss Snowden’s plans to steal NSA files? Did Applebaum suggest which items Snowden should take? Note that Applebaum is deeply involved with Wikileaks and has been a long-time, passionate defender of Julian Assange.
Glenn Greenwald revealed in his new book “No Place to Hide” that Snowden had used the code name “Cincinnatus” in early communications between the two. Interestingly enough, a “cyber-party” had been held in Hawaii in December 2012, and the host was someone who called himself “Cincinnatus.” Once this news came out, people began speculating on Twitter that perhaps this wasn’t a coincidence. Suddenly, on May 17, the cyber-party announcement was deleted by someone with the Twitter handle @jskuda. Fortunately Twitter user @ShrillBrigade located it on the Wayback Machine. And check out the title of Cincinnatus’ talk: “Painlessly setting up your own fast exit.” (h/t @catfitz)
Then yesterday, former criminal hacker and technical adviser to Greenwald and Poitras’ Freedom of the Press Foundation Kevin Poulsen published a limited hangout at Wired: Snowden’s First Move Against the NSA Was a Party in Hawaii.
It was December 11, 2012, and in a small art space behind a furniture store in Honolulu, NSA contractor Edward Snowden was working to subvert the machinery of global surveillance.
Snowden was not yet famous. His blockbuster leaks were still six months away, but the man destined to confront world leaders on a global stage was addressing a much smaller audience that Sunday evening. He was leading a local “Crypto Party,” teaching less than two dozen Hawaii residents how to encrypt their hard drives and use the internet anonymously.
“He introduced himself as Ed,” says technologist and writer Runa Sandvik, who co-presented with Snowden at the event, and spoke about the experience for the first time with WIRED. “We talked for a bit before everything started. And I remember asking where he worked or what he did, and he didn’t really want to tell.”
Runa Sandvik is a hacker who works at the TOR project along with Jacob Applebaum. TOR is a site (ironically funded by the U.S. Department of Defense) that provides free encryption software to people who want to hide their on-line activities (including drug dealers and child porn purveyors).
Poulsen writes:
The roots of Snowden’s crypto party were put down on November 18, 2012, when he sent an e-mail to Sandvik, a rising star in privacy circles, who was then a key developer on the anonymous web surfing software Tor.
Tor is free software that lets you go online anonymously. The software is used by a wide swath of people in need of extreme anonymity, including human rights groups, criminals, government agencies, and journalists. It works by accepting connections from the public internet, encrypting the traffic and bouncing it through a winding series of relays before dumping it back on the web through any of more than 1,000 exit nodes.
Most of those relays are run by volunteers, and the pre-leak Edward Snowden, it turns out, was one of them.
How about that? Snowden was already deeply involved with TOR in December 2012–and Jacob Applebaum of TOR just happened to travel to Hawaii a few months later in April! Coincidence? I don’t think so.
In his e-mail, Snowden wrote that he personally ran one of the “major tor exits”–a 2 gbps server named “TheSignal”–and was trying to persuade some unnamed coworkers at his office to set up additional servers. He didn’t say where he worked. But he wanted to know if Sandvik could send him a stack of official Tor stickers. (In some post-leak photos of Snowden you can see the Tor sticker on the back of his laptop, next to the EFF sticker).
Well, well, well. Now we know how Snowden got his TOR sticker. Did Runa give him the EFF sticker too? Read the rest of the Wired piece for more details.
Phew! I hope that made sense. This stuff is difficult to write about.
Also yesterday, well-known and respected journalist and New Yorker writer George Packer published a no-holds-barred review of Glenn Greenwald’s new book in the UK Prospect: The errors of Edward Snowden and Glenn Greenwald. Among other things, Packer accuses Greenwald of “a pervasive absence of intellectual integrity,” and provides numerous examples. He characterizes Snowden as someone who lives on the internet, detached from the realities of the real world. Here are a few excerpts, but please read the whole thing.
Snowden’s leaks can be seen, in part, as a determined effort to restore the web to its original purity—a project of technology rather than law. “Let us speak no more of faith in man, but bind him down from mischief by the chains of cryptography,” wrote Snowden, in an early message to his collaborators. In March of this year, appearing remotely from Russia on a robotised screen onstage at a TED talk in Vancouver, Snowden said that the single best solution to the NSA’s abuses is stronger encryption: “The internet that we’ve enjoyed in the past has been exactly what we, as not just a nation but as a people around the world, need.” In taking nearly two million highly classified documents from the US, he was grabbing back the key to heaven.
As I’ve written previously, Snowden’s solution to the problem of government interference with its citizens is impenetrable universal encryption–never mind the fact that this would allow vast numbers of vicious criminals to hide their actions from law enforcement.
As I suspected, Packer writes that Greenwald’s book “contains no major scoops.” He does, however, praise Greenwald’s argument for the primacy of privacy as central to a “free society.”
Greenwald also makes a powerful case—all the more so for being uncompromising and absolute—for the central role of privacy in a free society, and against the utilitarian argument that, since the phone companies’ metadata on Americans hasn’t been seriously abused by government officials (not yet, anyway), none of us should be too worried. In a chapter called “The Harm of Surveillance,” he cites Justice Louis Brandeis’s famous opinion on the basic “right to be let alone,” and writes: “The desire for privacy is shared by us all as an essential, not ancillary, part of what it means to be human. We all instinctively understand that the private realm is where we can act, think, speak, write, experiment, and choose how to be, away from the judgemental eyes of others. Privacy is a core condition of being a free person.”
I would argue that these considerations are of vital importance to people like Greenwald who are financially secure. Those Americans who must deal with racial and gender discrimination, long-term unemployment, and especially grinding poverty have other, more urgent concerns. Can one be a “free person” under those conditions?
Along similar lines, Packer writes:
If Greenwald and others were actually being persecuted for their political beliefs, they would instinctively understand that the rule of law has to protect people regardless of politics. The NSA disclosures are disturbing and even shocking; so is the Obama administration’s hyper-aggressive pursuit of leaks; so is the fact that, for several years, Poitras couldn’t leave or re-enter the US without being questioned at airports. These are abuses, but they don’t quite reach the level of the Stasi. They don’t portend a totalitarian state “beyond the dreams of even the greatest tyrants of the past,” as Greenwald believes is possible. A friend from Iran who was jailed and tortured for having the wrong political beliefs, and who is now an American citizen, observed drily, “I prefer to be spied on by NSA.” The sense of oppression among Greenwald, Poitras, and other American dissenters is only possible to those who have lived their entire lives under the rule of law and have come to take it for granted.
In the year since the first NSA disclosures, Snowden has drifted a long way from the Thoreauvian ideal of the majority of one. He has become an international celebrity, far more championed than reviled. He has praised Russia and Venezuela’s devotion to human rights. His more recent disclosures have nothing to do with the constitutional rights of US citizens. Many of them deal with surveillance of foreign governments, including Germany and Brazil, but also Iran, Russia, and China. These are activities that, wise or unwise, fall well within the NSA’s mandate and the normal ways of espionage. Snowden has attached himself to Wikileaks and to Assange, who has become a tool of Russian foreign policy and has no interest in reforming American democracy—his goal is to embarrass it. Assange and Snowden are not the first radical individualists to end up in thrall to strongmen.
Snowden looked to the internet for liberation, but it turns out that there is no such thing as an entirely free individual. Cryptography can never offer the absolute privacy and liberty that Snowden seeks online. The internet will always be a space controlled by corporations and governments, and the freedom it provides is of a limited, even stunting, kind. No one lives outside the fact of coercion—there is always a state to protect or pursue you, whether it’s Obama’s America or Putin’s Russia.
I’ve barely touched the surface of Packer’s scathing critique of Greenwald’s “journalism”; I enourage you to go to Prospect link to read more.
I have a few more stories for you that I’ll list link-dump style:
It appears that the prosecution in the Boston Bombing case decided to leak some previously secret information–most likely to counter the defense’s argument that Dzhohar Tsarnaev was illegally questioned by the FBI when he was in the hospital with terrible injuries.
Reuters: Accused Boston bomber admitted role in attack, prosecutors say
NBC News: Government doc shows how closely Boston Marathon bombers followed al Qaeda plans.
NY Daily News: Boston Marathon bombers used ‘sophisticated’ bombs made of parts from Christmas lights, model cars: prosecutors.
Boston Globe: Christmas Lights Used in Boston Marathon Bombs.
KSDK.com: Feds: Boston bomber’s hideout note says he wanted to be martyr.
ABC News: FBI Feared Boston Bombers ‘Received Training’ And Aid From Terror Group, Docs Say.
This is encouraging from the Boston Globe: Oakland Examining Pension of FBI Agent who Shot Todashev
Other News:
The Economic Times of India: Google wants to show ads through your thermostat and car. (You though the NSA was bad?)
Information Week: Google Outlines Advertising Vision. (How would you like targeted Google ads appearing on your refrigerator or watch?)
The Atlantic: It Wasn’t Household Debt That Caused the Great Recession; It was how that debt was disproportionately distributed to America’s most economically fragile communities.
NYT: U.S. Sends Troops to Chad to Aid Hunt for Nigerian Schoolgirls.
USA Today: Thai military declares coup, detains party leaders.
Science Recorder: ‘Aliens of the sea’ could lead to breakthroughs in regenerative medicine.
What stories are you following today? Please post your links on any topic in the comment thread.
Wednesday Reading: Wired Responds to Glenn Greenwald’s Critique of their Bradley Manning Coverage
Posted: December 29, 2010 Filed under: indefinite detention, torture, Wikileaks | Tags: blog wars, Bradley Manning, Glenn Greenwald, journalistic ethics, Julian Assange, Kevin Poulsen, Salon, Torture, Wikileaks, Wired Threat Level blog 18 CommentsGood Morning! Minkoff Minx is under the weather today, so I thought I’d write a little about the latest Wikileaks/Bradley Manning themed blog war between Glenn Greenwald of Salon and Kevin Poulsen of Wired.
Via Memeorandum, it appears that Glenn Greenwald struck a few nerves when he wrote his recent post accusing Wired of journalistic malpractice, because a response has been posted at the Threat Level blog.
Here is a bit of what Greenwald had to say:
For more than six months, Wired’s Senior Editor Kevin Poulsen has possessed — but refuses to publish — the key evidence in one of the year’s most significant political stories: the arrest of U.S. Army PFC Bradley Manning for allegedly acting as WikiLeaks’ source. In late May, Adrian Lamo — at the same time he was working with the FBI as a government informant against Manning — gave Poulsen what he purported to be the full chat logs between Manning and Lamo in which the Army Private allegedly confessed to having been the source for the various cables, documents and video that WikiLeaks released throughout this year. In interviews with me in June, both Poulsen and Lamo confirmed that Lamo placed no substantive restrictions on Poulsen with regard to the chat logs: Wired was and remains free to publish the logs in their entirety.
Despite that, on June 10, Wired published what it said was only “about 25 percent” of those logs, excerpts that it hand-picked. For the last six months, Poulsen has not only steadfastly refused to release any further excerpts, but worse, has refused to answer questions about what those logs do and do not contain. This is easily one of the worst journalistic disgraces of the year: it is just inconceivable that someone who claims to be a “journalist” — or who wants to be regarded as one — would actively conceal from the public, for months on end, the key evidence in a political story that has generated headlines around the world.
In June, I examined the long, strange and multi-layered relationship between Poulsen and Lamo, and in that piece raised the issue of Wired’s severe journalistic malfeasance in withholding these chat logs.
The Wired article is divided into two parts–the first part written by Wired editor Evan Hanson and the second part written by Poulsen. Greenwald’s point is that Wired is holding back on some of the evidence that led to Manning’s arrest. In his defense of Poulsen, Hanson skirts that issue by appearing to claim that only he and Poulsen know best which parts of the Manning-Lamo logs should be released to the public.
Armchair critics, apparently unhappy that Manning was arrested, have eagerly second-guessed our motives, dreamed up imaginary conflicts and pounded the table for more information: Why would Manning open himself up to a complete stranger and discuss alleged crimes that could send him to prison for decades? How is it possible that Wired.com just happened to have a connection with the one random individual Manning picked out to confide in, only to send him down for it?
Not one single fact has been brought to light suggesting Wired.com did anything wrong in pursuit of this story. In lieu of that, our critics — notably Glenn Greenwald of Salon, an outspoken Wikileaks defender — have resorted to shocking personal attacks, based almost entirely on conjecture and riddled with errors.
Of the chat logs, he writes:
We have already published substantial excerpts from the logs, but critics continue to challenge us to reveal all, ostensibly to fact-check some statements that Lamo has made in the press summarizing portions of the logs from memory (his computer hard drive was confiscated, and he no longer has has a copy).
Our position has been and remains that the logs include sensitive personal information with no bearing on Wikileaks, and it would serve no purpose to publish them at this time.
That doesn’t mean we’ll never publish them, but before taking an irrevocable action that could harm an individual’s privacy, we have to weigh that person’s privacy interest against news value and relevance.
This is a standard journalistic balancing test — not one that we invented for Manning. Every experienced reporter of serious purpose recognizes this, and the principal is also embodied in the Society of Professional Journalists’ code of ethics:
Recognize that gathering and reporting information may cause harm or discomfort. Pursuit of the news is not a license for arrogance…. Only an overriding public need can justify intrusion into anyone’s privacy. Show good taste. Avoid pandering to lurid curiosity.
Hansen claims that Wired is protecting Manning’s privacy by their refusal to publish the remaining 75% of the logs that they have kept secret. But why should we believe that? Aren’t they really protecting Lamo while he (as Greenwald argues), as the only source of knowledgeable information about the contents of the logs:
has been allowed to run around making increasingly sensationalistic claims about what Manning told him; journalists then prominently print Lamo’s assertions, but Poulsen’s refusal to release the logs or even verify Lamo’s statements prevents anyone from knowing whether Lamo’s claims about what Manning said are actually true.
In addition, Greenwald argues that:
There are new, previously undisclosed facts about the long relationship between Wired/Poulsen and a key figure in Manning’s arrest — facts that Poulsen inexcusably concealed [and] Subsequent events gut Poulsen’s rationale for concealing the logs and, in some cases, prove that his claims are false.
And on top of all that, Greewald points out that Poulsen himself reported that Lamo is a “convicted felon” who was “involuntarily hospitalized” for psychiatric problems shortly before his on-line interactions with Manning.
In the second part of Wired’s defense, Poulsen claims that Greenwald’s accusations against him are based on false information:
On Monday, Salon.com columnist Glenn Greenwald unleashed a stunning attack on this publication, and me in particular, over our groundbreaking coverage of WikiLeaks and the ongoing prosecution of the man suspected of being the organization’s most important source. Greenwald’s piece is a breathtaking mix of sophistry, hypocrisy and journalistic laziness.
I can’t wait for Greenwald’s response to that!
Poulsen’s piece is basically a screed in which he accuses Greenwald of multiple violations of journalistic ethics. Poulsen discusses his long-time relationship with Lamo, but as far as I can tell, Poulsen’s only information about Manning comes secondhand from Lamo.
Wired.com was the first to report, last June, on the then-secret arrest of Pfc. Bradley Manning. I learned of the arrest from Adrian Lamo, a well-known former hacker on whom I reported extensively from 2000 to 2002. It was Lamo who turned Manning in to the Army and the FBI, after Manning — isolated and despondent — contacted him online and began confiding the most intimate details of his life, including, but by no means limited to, his relationship with WikiLeaks, and the vast databases he claimed to have provided them.
Co-writer Kim Zetter and I followed up the story four days later with a piece examining Manning’s motives. The Washington Post had just run a fine story about Manning’s state-of-mind: At the time of his discussions with Lamo, he’d been through a bad breakup and had other personal conflicts. But I felt — and still do feel — that it’s a mistake to automatically ascribe Manning’s actions to his feeling depressed. (For one thing, his breakup occurred after the leaking.) There’s an implicit political judgment in that conclusion: that leaking is an aberrant act, a symptom of a psychological disorder. Manning expressed clear and rational reasons for doing what he did, whether one agrees with those reasons or not.
So we went into the logs of the chats Manning held with Lamo — which Lamo had provided Wired and The Washington Post — and pieced together a picture of why Manning took his historic actions, based on his own words (“Suspected Wikileaks Source Described Crisis of Conscience Leading to Leaks”). As a sidebar to the article, we published excerpts from those chat logs.
Poulsen argues that “everything of consequence” about Manning from the logs has already been published. But why should we believe Poulsen when he has a long-time relationship with Lamo and no relationship with Manning?
You’ll have to read the rest to get the entire convoluted explanation. Most troubling to me is that neither Hansen nor Poulsen mentions the treatment that Manning is getting in prison–that by any civilized country’s standards, he is being tortured.
We’ll have to stay tuned for Greenwald’s response to all this. I’ll bet it will be a doozy. Meanwhile, what do you think?
————————————————————————————————————————————-
UPDATE 1 9:42AM Eastern: Greenwald has a response up now. He begins with this:
Last night, Wired posted a two-part response to my criticisms of its conduct in reporting on the arrest of PFC Bradley Manning and the key role played in that arrest by Adrian Lamo. I wrote about this topic twice — first back in June and then again last Sunday. The first part of Wired’s response was from Wired.com Editor-in-Chief Evan Hansen, and the second is from its Senior Editor Kevin Poulsen. Both predictably hurl all sorts of invective at me as a means of distracting attention from the central issue, the only issue that matters: their refusal to release or even comment on what is the central evidence in what is easily one of the most consequential political stories of this year, at least.
That’s how these disputes often work by design: the party whose conduct is in question (here, Wired) attacks the critic in order to create the impression that it’s all just some sort of screeching personality feud devoid of substance. That, in turn, causes some bystanders to cheer for whichever side they already like and boo the side they already dislike, as though it’s some sort of entertaining wrestling match, while everyone else dismisses it all as some sort of trivial Internet catfight not worth sorting out. That, ironically, is what WikiLeaks critics (and The New York Times’ John Burns) did with the release of the Iraq War documents showing all sorts of atrocities in which the U.S. was complicit: they tried to put the focus on the personality quirks of Julian Assange to distract attention away from the horrifying substance of those disclosures. That, manifestly, is the same tactic Wired is using here: trying to put the focus on me to obscure their own ongoing conduct in concealing the key evidence shining light on these events.
In a separate post, I fully address every accusation Hansen and Poulsen make about me as well as the alleged inaccuracies in what I wrote. But I’m going to do everything possible here to ensure that the focus remains on what matters: the way in which Wired, with no justification, continues to conceal this evidence and, worse, refuses even to comment on its content, thus blinding journalists and others trying to find out what really happened here, while enabling gross distortions of the truth by Poulsen’s long-time confidant and source, the government informant Adrian Lamo.
The link to Greenwald’s previous post goes to “page not found.” I’ll update when he fixes the link. About the substance of the argument between Greenwald and Poulsen, Greenwald writes:
The bottom line from Hansen and Poulsen is that they still refuse to release any further chat excerpts or, more inexcusably, to comment at all on — to verify or deny — Lamo’s public statements about what Manning said to him that do not appear in those excerpts. They thus continue to conceal from the public 75% of the Manning-Lamo chat. They refuse to say whether Lamo’s numerous serious accusations about what Manning told him are actually found anywhere in the chat logs. Nor will they provide the evidence to resolve the glaring inconsistencies in Lamo’s many public tales about the critical issues: how he came to speak to Manning, what Lamo did to include these disclosures, and what Manning said about his relationship to WikiLeaks and his own actions. Every insult Wired spouts about me could be 100% true and none of it changes the core fact: Wired is hiding the key evidence about what took place here, thus allowing Lamo to spout all sorts of serious claims without any check and thus drive much of the reporting about WikiLeaks.
UPDATE 2: Jane Hamsher also has a post up on this story. She writes:
You would have to have been f&#%ing r#*&rded to believe that in an era of unprecedented intolerance for press leaks of any kind, that the U.S. Army Criminal Investigation Division, the FBI, the NSA, the U.S. Air Force Office of Special Investigations and the Cyber Defense Crime Center knowingly and willingly not only allowed convicted hacker Adrian Lamo to hold on to chat logs that contained sensitive classified information, but to distribute them unexpurgated to the press.
I only see two possibilities. One, Wired had the chat logs before Lamo made any calls to authorities, and was a party to whatever subsequently happened. Or two, the copies of the chat logs that have been given to the press have been done so at the instigation of the US government, and with their full approval.
Of course there’s always c) all of the above, which is what I’m guessing is the most likely scenario.
Firedoglake has posted a database of all the available information on interactions between Manning, Lamo, and the U.S. government.
Stay tuned….








Recent Comments